- Google is banning Flash-based advertising. About damned time. Flash is and has always been a malware farm. Die, monster, die!
- Flash is the biggest risk but not the only one in terms on online ads. AdBlock Plus is very good, but makes its money by selling whitelist positions to advertisers like Taboola. Here’s how to turn off the whitelist.
- Although he doesn’t say much about it in the article itself, I see this research about the hypothalamic attack region as justification for considering tribalism born and not learned behavior. (Thanks to Tom Roderick for the link.)
- The BMI is a lie, and a deadly one. A measurement that cannot distinguish between fat and lean muscle is a lie now, has always been a lie, and will never be anything other than a lie. Furthermore, it’s been a lie for 185 years. You’d think medical science would have figured it out by now.
- Solar Cycle 24 is the weakest in 200 years. Bummer. First time I can have a reasonable HF antenna in 13 years, and it may not matter. But at least I’m now living in a warm climate.
- Nonetheless, the Sun seems remarkably active in this video showing an entire year of solar activity at 12 seconds per frame.
- What if NASA designed space travel posters? Well, um, they did. (Thanks to Pete Albrecht for the link.)
- Engadget reviews the second-gen Compute Stick 2016, which is a Windows 10 computer the size of a fat thumb drive that plugs into your TV’s HDMI port. HDMI doesn’t supply power (yet, but MHL is coming) so you still need a wall wart. However, it’s now got 2 USB ports so you can plug both keyboard and mouse into it without a hub. (Many keyboards now have USB hubs, so if you want you can put both on a single port just using the keyboard hub.) Even thought it’s as small as it is, it still has a fan. Wow.
- How they build a tunnel with giant concrete Legos and a truck with casters where a hedgehog has spines.
- The Senate has made the ban on Internet access taxes permanent. Note that this has nothing to do with sales taxes on Internet purchases, but is about taxing Internet access itself. The law, originally passed in 1998, had to be renewed annually. If the House passes it and the President signs it, the law will no longer need to be renewed every year.
- People ask me sometimes why I consider Woodrow Wilson by far the worst US President in history. Here’s only one reason. There are many more. Here’s another. He came as close to being the first American dictator as we’ve ever come. (Thanks to Esther Schindler for the first link.)
- Neanderthal genes may be a mixed bag. Well, sweetheart, what isn’t?
malware
Odd Lots
The March of Computer Time
Last night I turned in my chapter on programming–just think, all of software development summarized in 55 book pages!–and am gathering my thoughts on mass storage for the chapter I’ll begin later today or tomorrow. Again, if you haven’t seen me much lately that’s the reason.
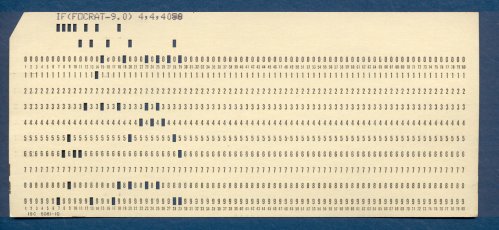
Each of my chapters has begun with a historical perspective on that chapter’s computer technology topic. This has brought lots of things to mind that I haven’t thought about in years, like IBM cards, FORTRAN, punched tape, and Bernoulli Boxes. I still have the card deck from the first program I ever wrote, in the spring of 1970. (See above.) I did some work with paper tape as well in my COSMAC days, but whatever tape I kept has been hiding well. I’d love to get a scan of a length of ASR-33 style punched tape, or a length (8″ or so) of the tape itself to scan here. Doesn’t matter what’s on it as long as it’s not greasy or physically damaged. Contact me if you have some you could spare, or least scan.
Time marches on. I have a 10MB Bernoulli Box cafeteria tray cartridge–probably in a box somewhere with the paper tape–and an original 1983 Microsoft Mouse. Obsolescence doesn’t bother me as long as I can keep functionality. I had to buy a copy of Office 2007 to keep writing commercially, since Word 2000 doesn’t understand .docx files, and Atlantis doesn’t do annotation. Yup, time marches on.
It does. Right now we’re looking down the throat of something a little unprecedented: On April 9, Microsoft turns off security updates for Windows XP.Most of my nontechnical friends seem unaware of this, and my nerd friends have long since moved on to Win7 or 8. I’m in the middle: I’ve been using Win7 on my GX620 for about a year, and have a new Win7 Optiplex 780 on the shelf ready to be populated and configured when time allows. (I’ve done almost nothing but this book for what seems like–hell, has been!–months.) I’m about to take my quadcore in for a new sled-mounted SSD and Windows 7 Pro. The 780 will become Carol’s office machine. I will keep an SX270 XP machine basically forever, because it has pop-in drives for both 3.5″ floppies and Zip cartridges, some of which are piled in odd boxes here for no compelling reason other than they’re paid for. (Yes, most of them have probably gone to bitrot by now.) However, it will no longer be on my network, and will be powered up only as needed.
Here’s an interesting wrinkle that few people seem aware of: Win7 Professional comes with a special-purpose copy of VirtualPC, with a VM containing an instance of XP. (Win7 home does not.) I’m thinking that if I don’t enable the Ethernet connection to the XP VM, it doesn’t matter whether the instance gets security updates or not. I have some stuff here that won’t run on Win8, and possibly not on Win7 either. I can install it on my poor SX270 survivor, of course, but it will be interesting to see what limitations may exist on the XP VM. If something weird turns up in the VM, I can always revert to an archival image.
The real problem with this, of course, is that a lot of nontechnical people are still using ancient machines that won’t run Win7 ever. Only five or six years ago, I still saw Windows 95 on 486 machines owned by older people at my parish. I’ll bet there are plenty of doddering Pentia XP boxes with 512MB of RAM still crunching email and (maybe) Web, along with Office 97. What happens to them? They may well get pwned. On the other hand, I’ve seen several with updates turned off that aren’t pwned. How bad is the problem, really?
I’m sure nobody knows. Sometime this spring we’re going to find out. How many exploits are likely to be left in a 12-year-old codebase? There will be some. Not all exploits are the result of bad coding practices, though I’m sure plenty can be walked back to unbounded string functions in libc, which the C community just can’t seem to give up. XP’s security model is generally lousy, especially for people who don’t understand the implications of what they do, double-especially with Internet-facing apps. That being the case, how far does Microsoft’s responsibility extend? As big as they are, can’t they keep a few security fanatics on staff to fix the exploits that do appear?
I’m thinking that questions like this may soon be asked in the courts of law. We’ll see.
Anyway. I can fix things here, and in extended family. I do worry about nontechnical retirees at our church and elsewhere. When you’re 80, a 12-year-old OS may not seem like any kind of problem, and those on fixed incomes may not feel like $500 for a new box is worthwhile to solve a problem that remains hypothetical. (Hell, my 4Runner is older than XP.) Those of us who remember Y2K hysteria can be forgiven for a strong dose of skepticism. I expect pwnage. There’s pwnage today. The only question is how bad it gets, and how much bad PR it will earn Microsoft. My prediction: If it gets bad enough, and the lawsuits get thick enough, the updates will return.
Pass the popcorn and dig your 3-D glasses out of the drawer. This is gonna be good.
Spam Supposedly from Facebook Friends
As mysteries go this was small change, but I stumbled across its solution earlier today: spam nominally from Facebook friends. I’ve been getting a recognizable species of link spam every day or two for a couple of months now. The From: field always contains the name of someone I know. The From: email address, however, is unknown to me and does not belong to the person named. The Subject: field is short and nondescript, like “Hello”. The body of message is brief and follows this form:
super http://spammityspam.spam/goosebrow/53zappovat/
11/21/2012 10:33:27 AM
The From: email address is always a gobbledegook address from a big email service like Hotmail or AOL. There may be two or three words before the link, but no more than that. The link destination is different every time. I don’t know, don’t care, and don’t intend to find out what’s at the other end of the links.
I first assumed that someone I knew had gotten his or her address book hijacked by a trojan, which has long been a common practice when a machine is hacked. The interesting thing was that many of the people didn’t know one another at all. (I asked a few of them.) My next thought was that my own address book had been hijacked, except that two other people (out of eight or nine spams that I had tucked away to examine) were folks for whom I did not have and never had an email address. It took awhile for me to realize that the only common element was their presence in my Facebook friends list.
Bingo.
I sniffed around and found a nice description of the problem on CNET. In short, there was a Facebook vulnerability that allowed a scraper to lift the names (but not the email addresses, nor any private information) from my facebook friends list. Facebook has fixed the vulnerability, or claims to have fixed it. Facebook being Facebook, however, I’m sure there are plenty of others down there in the morass.
Given that over half of the posts in a recent sample of my friends feed today were idiotic or hate-filled images (many images consisting solely of words, which is idiocy cubed, and sometimes words too small to read, which is idiocy to the seventeenth power) I wonder sometimes why I bother.
The Trojans Are Winning
Trojans sent as spam attachments are (thankfully) not as common as they used to be. Several years ago I would get fifteen or twenty every day. In the past year or so I only get three or four per week. Nearly all of them are executables of some kind, either simple Windows .exe or .scr files, or else an MS Office file (generally an Excel spreadsheet) containing a malicious script. This morning I got a flurry of phishing attempts delivered as PDF files. As I often do, I scanned the PDF file with both AVG and MalwareBytes to see which trojan was present. This time I got a negative from both utilities.
Now, an email telling you that you should open the attached file to see details of your order / bank transaction / payroll deposit etc. are guaranteed to be malware. If two well-regarded AV utilities call the file clean, I begin to wonder how effective our AV technology really is. I’m particularly disappointed in MalwareBytes, which has been razor-sharp so far at detecting email malware.
So I submitted the file to Jotti, which is an interesting one-file-at-a-time malware scanning service. I’ve known about it for some time but never tried it before, as I’d never received anything that managed to duck AVG and MalwareBytes both. What Jotti does is aggregate online file-scanning services, and then aggregate the results from all the services. The PDF exploit got past 14 of 20 scanning services used by Jotti, including AVG. Them’s lousy numbers.
Here’s a screen cap of the Jotti output report.
To get some perspective, I did a little additional testing. Things got worse. I saved a .zip payload out of an obvious phish email that came in yesterday, and submitted the zip to Jotti. One out of twenty scans came up positive. I then (carefully) unzipped the payload to a naked .exe, and submitted that. Zero. Zip. Nada. Nobody caught it. Wow.
What this tells me is that the Trojans are winning. Scanning things before you open them is no longer any sort of guarantee. Dodging malware now requires that you turn your paranoia knob up several notches. Here’s what I recommend for Windows users:
- Run Internet-facing apps from an LUA, or with a privilege-limiter like DropMyRights.
- Install and use NoScript, and allow scripting only on trusted sites. Be conservative on what “trusted” means. Javascript is evil.
- Install and use AdBlock Plus. Until sites can guarantee that their ads aren’t serving up malware, I reserve the right to block their ads. It isn’t just small sites that are vulnerable; Gawker Media got hit a year or two ago.
- Do not use Adobe Reader. There are lots of other PDF readers that are as good or better. I recommend PDF XChange from Tracker Software. What you want is a high-quality product with low market share. Adobe Reader is an exploit farm in part because the bad guys search it harder for exploits–and most of the exploits are highly specific to Adobe Reader.
- Whatever PDF reader you choose, go to the options dialog and turn off Javascript. I have yet to hear any compelling reason for a PDF to execute JavaScript. Oh, and did I say that Javascript is evil?
- Do not use Flash on a Windows system. Don’t even install it. Use a Linux instance to read YouTube or other Flash-based sites that you absolutely must browse.
- If you’re geeky enough, get a VM manager and run Internet-facing apps (or at least Flash-equipped sites) from inside a VM. This makes bookmarking tricky, but a VM is a very tough thing for malware to get out of.
- Don’t pirate software. In particular, don’t install something and then go looking for a crack to get past registration/activation. Cracks are virtually always malware, and the pirated apps themselves are infected as likely as not.
- It sounds nuts, but we do it: Get an entirely separate machine for any kind of online banking. Ours runs Linux. We do nothing on the machine at all other than online banking. We turn it off except when it’s in use, which is an hour or two per week, tops.
Both Macs and Linux machines are harder to infect than Windows, but most of their supposed immunity comes from their being scarce enough that the bad guys don’t attempt to exploit them. I’ve seen a troubling increase in the number of exploits tuned for the Mac, which means that Macs are now mainstream. With success comes danger. Also, more and more malware comes in via social engineering, and since that’s a wetware problem, Macs and Linux boxes are no more immune to that than Windows. (The real malware danger in running a Mac is the all-too-common conviction that Macs are immune to malware. Uh-uh.)
It’s certainly true that the vast majority of malware infections are the result of Computing While Stupid. Alas, the line we’ve heard for years about keeping AV software installed and up-to-date is increasingly irrelevant. There is no way to harden a PC to allow you to do any damned thing you want. Nothing’s bulletproof. You have to dodge–and you have to dodge harder and harder all the time.
Odd Lots
- Here’s another take on the EasyBits GO debacle, from a guy who used to work at Easybits. Even if it’s not a trojan, it’s still crapware, and careless crapware at that. The Microsoft connection is intriguing: MS will soon be reviewing the entire Skype ecosystem, and may decide to do some decontamination. I don’t think it will go well for EasyBits.
- Down in the trenches in the Carb Wars, people who yell, “A calorie is a calorie! It’s just the laws of thermodynamics!” don’t understand thermodynamics. I’ve known this for years. Here’s a good explanation. (Thanks to David Stafford for the link.)
- Mike Reith saw a pure white squirrel awhile back, up near Denver. I had never heard of non-albino white squirrels before, but they exist, and appear to be spreading due to evolutionary selection–by humans.
- Maybe it wasn’t us who extinctified the Pleistocene megafauna. (Or at least our paleolithic ancestors.) Maybe it was the Sun. Scary business. (Thanks to Jim Strickland for the link.)
- From the Words-I-Didn’t-Know-Until-Last-Week Department: prosopagnosia, the inability to recognizes faces or familiar objects. (Thanks to Bruce Baker for calling it to my attention.)
- From Pete Albrecht comes a link to a video of a train wreck caused by a tornado–with the wrinkle that the wreck is filmed from a security cam on one of the freight cars. Toward the end we see a derailed tanker striking sparks as it’s dragged against the rails. Made me wonder what would have happened had it been full of LP gas…
- Forgive the vulgarity and the pervasive comics/movies influence, but this is a point that needs to be made, and textual fiction is no exception. (Thanks to Frank Glover for the link.)
- I like sprouts. I haven’t eaten them for ten years. Here’s why. Alas, being organic doesn’t help. (Thanks once again to Pete.)
- Here’s a cogent (and funny) illustration of a great deal of what’s wrong with science these days. Hint: It’s not science. Most of the problem is the butthead festival we call the media. (The rest is the grant system.)
Skype and EasyBits: Mistake or Attack?
After a strange reluctance to jump on the issue, the major news outlets have begun covering the excitement of this past Saturday morning, when untold numbers of Skype users suddenly found new software installed on their Windows PCs, without so much as a notification or request for permission from Skype. Skype has been almost silent on the issue, as has the firm that originated the software in question, EasyBits GO. EasyBits is not obviously malware, but there were some weird EasyBits/Skype connections with malware last year, and Saturday’s install certainly acted like malware. So was it a mistake? Or was it an attack? The greatest weirdness of all is that we still don’t know.
My take? It looks like a mistake. It smells like an attack.
I set up an old XP machine with Skype on it Saturday afternoon, and left Skype running in a window. It’s still running as I write, and there’s no trace of the EasyBits installer. I thought the fact that it was still at SP2 might have made a difference, but I’ve heard from people who got the install on SP2 machines. This suggests that Skype immediately stopped pushing installs once the crap started to fly online, which further suggests that Skype was in control and that it was a mistake rather than an attack.
There’s a tendency to love a great story, and we have to be careful not to read more into things than reality warrants. I’m an SF writer, and the futures I’ve tried to predict (as have many other, far more notable SF writers than I) have turned out to be a lot more dramatic and colorful than the future that actually worked itself out over the years. We underestimated small things (computers) and way overestimated big things, like space travel and (yes indeedy!) flying cars.
Here’s an example of wearing your SF hat too much: Some years back, I was predicting that malware authors would create trojans that very quietly installed file-sharing nodes behind the screen of rootkit techniques, which would then search for sharable content on the machine and then open LimeWire-style P2P connections to the Net at large. Because it was a trojan, it would provide plausible deniability in copyright infringement lawsuits–and because it provided plausible deniability for file-sharing, people would deliberately infect their machines with it. The trojan would soon be on over a billion machines, and Big Media could do nothing at all about it.
That would have made a great cyberpunkish story; maybe I should still write it. But it didn’t happen, and I think it won’t happen. Malware authors are well past this sort of Merry Pranksters stage. Malware happens for one reason only: Money. If there’s no way to monetize a malware scheme, it won’t be written. So with anything like the Skype Affair, you have to look for the money. Crapware still seems to be the likeliest explanation: EasyBits could have paid Skype by the install to push down a new version of its games platform, and make it look like a normal Skype update. Stupidity intervened, which happens all the time. (Google “Sony Rootkit” to see only one example, and certainly the stupidest. Bruce Schneier has what I consider the last word.)
That said, there’s still the possibility that a server-side infection was behind the push, and that what we got was a compromised version of EasyBits that may at some later time (patience, patience!) download the Real Deal, whatever that Real Deal might be. And whatever it is, it’ll be about money.
The end of the story hasn’t been written yet. Keep your virus checkers handy. Consider Skype alternatives. (Look into Jitsi.) And stay tuned.
Odd Lots
- Heads up here; this is important: Something called EasyBitsGo.exe appeared in a directory under Documents and Settings/Application Data/All Users this morning about half an hour ago. The executable was already installed and running and wanted permission to install Flash Player. (I do not allow Flash Player on Windows machines, as it’s exploit fertilizer.) The timestamp on the executable’s directory tree indicated that it had been installed no more than a minute before it popped up. There appears to be a Skype connection, and I was using Skype at the time. Be careful. If you see it, close Skype, kill the easybitsgo.exe process in Task Manager to close it, and then nuke that directory. Then go to Add/Remove Programs and uninstall it. Reboot. If Skype did in fact install this thing without asking, it may be the beginning of the end of my own use of Skype.
- Per the above: Launch Skype. Select Tools | Options | Advanced, and un-check Automatically Start Extras. Then reboot again and make sure it’s not still running.
- All RAMmed up and nowhere to go: KingMax has announced a 64GB MicroSDXC card…and there’s almost nothing on the market that will use that much storage in one chunk. If we’ve learned nothing else in the last thirty years, it’s that “barriers” are a mark of either hardware vendor cheapouts, or software vendor incompetence. Are address lines so dear that we can’t raise the barriers to a level at least five years out? (I suggest 256 TB. Ok, six or seven years out.)
- What if Babbage had outsourced tech support to the Pacific Rim? (Thanks to Ernie Marek for the link.)
- Yet another longstanding dietary fetish is now in jeopardy. The case against salt always looked weak to me, in that it was clearly hazardous to people who already had certain kinds of heart disease, but that the case that it caused heart disease was mighty thin and mostly anecdotal. All roads continue to lead back to carbs, and especially sugar. More in coming days as time allows. (Thanks to Carol for the link.)
- If just rooting your Nook Color isn’t quite enough, here’s a description of how to turn it into a complete Android tablet. If it sounds scary to you, well, you may not have the computing experience to do it; but when I read the article I thought, Sheesh, that’s easy. You can even boot from the SD slot to get a sense for the mod before making changes to device memory. The process appears to be reversible, and the mod allows you to use Bluetooth-capable GPS receivers and other Bluetooth devices. Given how cheap the NC is, I’m tempted to try it while I wait for the high-end slates like Xoom to mature.
- We could maybe use a few more of these.
Odd Lots
- Several people have asked why I didn’t post any photos from the big 4-day dog show in Denver, and I must admit (with profound annoyance) that my camera bag vanished sometime on Monday, and both of my digital cameras were in it. That’s a Canon G10 and a Nikon CoolPix S630, and with the biggish SD cards I put in them, it’s close to a $1000 loss. Neither the hotel nor the National Western Complex recovered the bag, so I can only assume it was stolen during the show, and with it went all the photos we took through Sunday night.
- Slashdot reports that 80% of all software exploits during the fourth quarter of 2009 were malicious PDF documents. I’ve been a Foxit user for some time, but as Foxit becomes more popular, the bad guys will begin exploiting its flaws as well. (There is evidence that this has already happened.) It may be time to test software like Evince and Sumatra, both of which are available for Linux and Windows.
- As I write this, you have eight hours to bid on the Compaq II machine that Anders Hejlsberg used to develop Turbo Pascal 4.0. The proceeds from the auction go to the Clinton Bush Haiti Fund. It’s one of those green-screen luggable that I always admired, but bidding is currently at $2025, yikes. (Thanks to the many who pointed this out, with Larry O’Brien being the first.)
- Something confirming a phenomenon that I’ve noticed: Food expiration dates are conservative, and most food is good for a reasonable period after they supposedly time out. Still, after expiry, your nose is your stomach’s best friend.
- For whatever it’s worth, here’s a list of the top-grossing movies of all time, with inflation-adjusted values. (Thanks to Frank Glover for the link.) Unsurprisingly, Gone With the Wind still beats all comers with a mind-boggling 1.5 billion dollars, the though the original Star Wars is right behind it at $1.3B. What’s worth noting is that all but six films in the top 14 were either Disney animation or special-effects extravaganzas. (It’s all but five if you think the opticals in The Ten Commandments were significant, as I do.) Lesson: We don’t go to the movies to watch unpleasant people screaming at one another.
- Also from Frank comes a pointer to a short item suggesting that we kiss to enforce reproductive monogamy by developing immunities to one another’s specific viruses. I’m not sure I buy it either, but evolution has done far weirder things than this.
Odd Lots
- I just missed seeing a nice article on the current sunspot dearth before posting my entry for August 20, 2009. The longest stretch this solar minimum is 52 days back in 2008, and we could well exceed that come early September with no additional spots. (We’re now at 45 consecutive spotless days.)
- I’m practicing rolling my eyes for the latest showing of the Mars hoax. On August 27, multitudes of people who are rumored to posess something close to human intelligence are claiming that Mars will appear the size of the full Moon. (This does the email rounds every couple of years.) Note well that if Mars were the size of the full Moon in the sky, we’d be living a disaster movie, so be very glad it’s a hoax.
- Stanford University reports that media multitaskers do not in fact multitask very well. I liked this refreshingly straightforward quote in the article: “We kept looking for what they’re better at, and we didn ‘t find it.” More details here from the Beeb.
- ZDNet reports on a virus, named Win32.Induc, that pulls a trick I’ve never heard of before: It looks for the Delphi programming environment, and infects Delphi such that any apps built by that copy of Delphi will carry the virus. I can’t quite see how this manages to propagate in a herd as thin as the Delphi programming world has become, unless Delphi programmers tend to use a lot of Delphi utilities obtained from places like Torry’s. (I know I did, so that’s my theory.)
- Maybe you had one: A die-stamped thin steel rectangular lunchbox, usually (but not always) with completely inane artwork, often branded to TV shows, toys, and other pop-culture phenomena. The Denver Westword has a “10 worst” feature on tin lunchboxes that’s worth a look. I never carried a tin lunchbox to school (we used paper bags from Certified) but I have one now very much like #1, purchased at a hamfest years ago, filled with FT-243 ham-band crystals. I’ve always wondered why the boxes always had little vents punched in the short end sides.
- Here’s an interesting 2-tube minimal broadcast-band superhet, using 12V space-charge tubes. It’s interesting enough that I might even build one, though my own holy grail is a 2-tube FM receiver. I’ve got the schematic (courtesy John Bauman KB7NRN) and lack only the time to hack it together.
- I’d never heard of morning glory clouds, probably because they mostly happen in a certain part of Queensland, Australia. The bigger question is why they get all the truly great Weird Stuff down there, and we have to settle for minor-league weirdness like Michael Jackson.
Odd Lots
- From the Words I Didn’t Know Until Yesterday Department: “charcuterie,” meaning cured meats like bacon, ham, prosciutto, and the preparation thereof.
- I talked to the realtor who’s handling the listing of the old Heinlein house here in Colorado Springs. What she said astounded me: Heinlein’s 1950 custom house is still in there. They built that ugly thing around it in 1995 or so. Parts of the original structure were removed, but most of it still exists, although it evidently was used as framing more than anything else.
- And further relevant to the Heinlein House is a report from elder SF fan Bruce Pelz, who not only visited the house in Colorado Springs in 1963 when the Heinleins were still living there, but he slept in their legendary fallout shelter. (Cool photo there–definitely click through! And thanks to Bruce Baker for the link.)
- Needless to say, I haven’t visited the Heinlein fallout shelter (I stood in line to shake the great man’s hand at MidAmericon in 1976, and that was the only time I ever met him) but I frequently visited the 10-foot-deep underground fallout shelter of the late William A. “Bill” Rhodes in Phoenix, which he was using as a cool (literally) computer room until his death in 2006. It was culturally jarring–people of my parents’ generation took fallout shelters for granted, and people of my generation (for the most part) found them appalling.
- CFLs may not be the big environmental win that they’re being touted as, because the power factor of the lamps is very low. Thery’re still a win, but the hype needs to be pruned back a little.
- The whole idea of a CAPTCHA may be flawed, and although there are a number of objections to CAPTCHAS, this article pins down the primary and probably unfixable one: You can pay people to solve them. There are apparently some porn/pirate sites that charge for access in solved CAPTCHAS. And if nothing else works, hire a CAPTCHA-breaking firm in the third world. It looks to me like CAPTCHAs are becoming at best speed-bump hindrances to bots. If I had to guess, I’d say make it slower to establish accounts, and certainly slower for one IP to sequentially attempt a CAPTCHA. Could teergrubing make a comeback?
- For the benefit of those who asked, here is the Web site of the people who did my crowns over this past year. They are artists, especially Dr. Frank Seaman. The 15-month project was actually a collaboration between two independent offices in the same building. Dr. Jeanne Salcetti did the periodontal portion (gingivectomy, tooth extraction, bone graft, and implant) and she was wonderful too. I recommend both of them without hesitation.